Maritime cyberattacks surged 103% in 2025, rising to 828 incidents from 408 the year before — and the systems most exposed are the ones oldest: legacy ship management platforms built before 2015. The conversation around modernisation is no longer about technology preference or budget timing. It’s about survival.
But here’s what most maritime decision-makers don’t realise: the cost of running legacy ship management software has already exceeded the cost of replacing it. The licence fee is just the visible fraction.
This post pulls back the curtain on the five hidden cost categories driving the real expense of legacy systems — and introduces the “Modernisation Window”: why 2026 is the last year the cost of acting is lower than the cost of waiting.
Beyond the Licence Fee: The Five Hidden Cost Categories of Legacy Ship Management Software
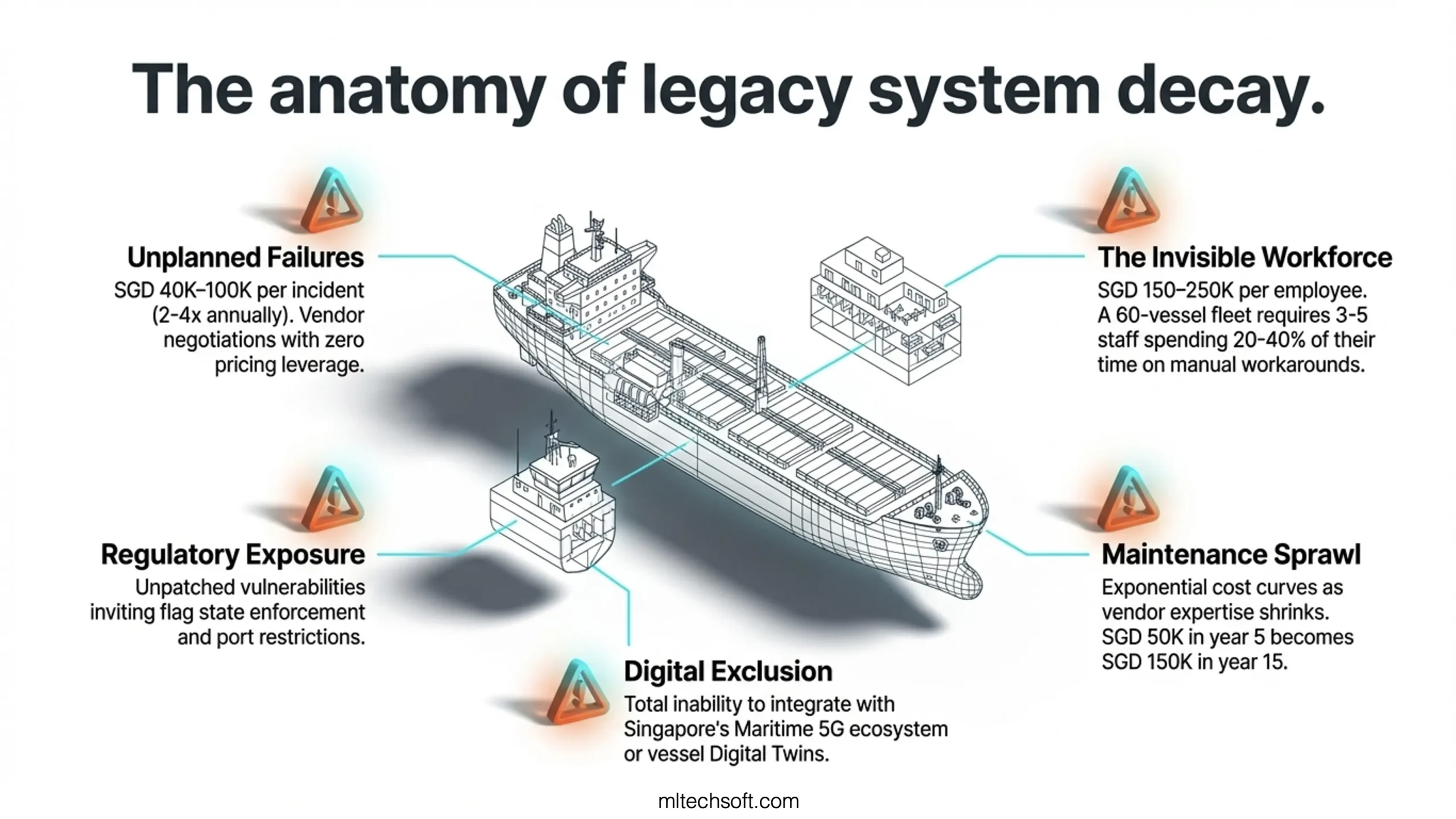
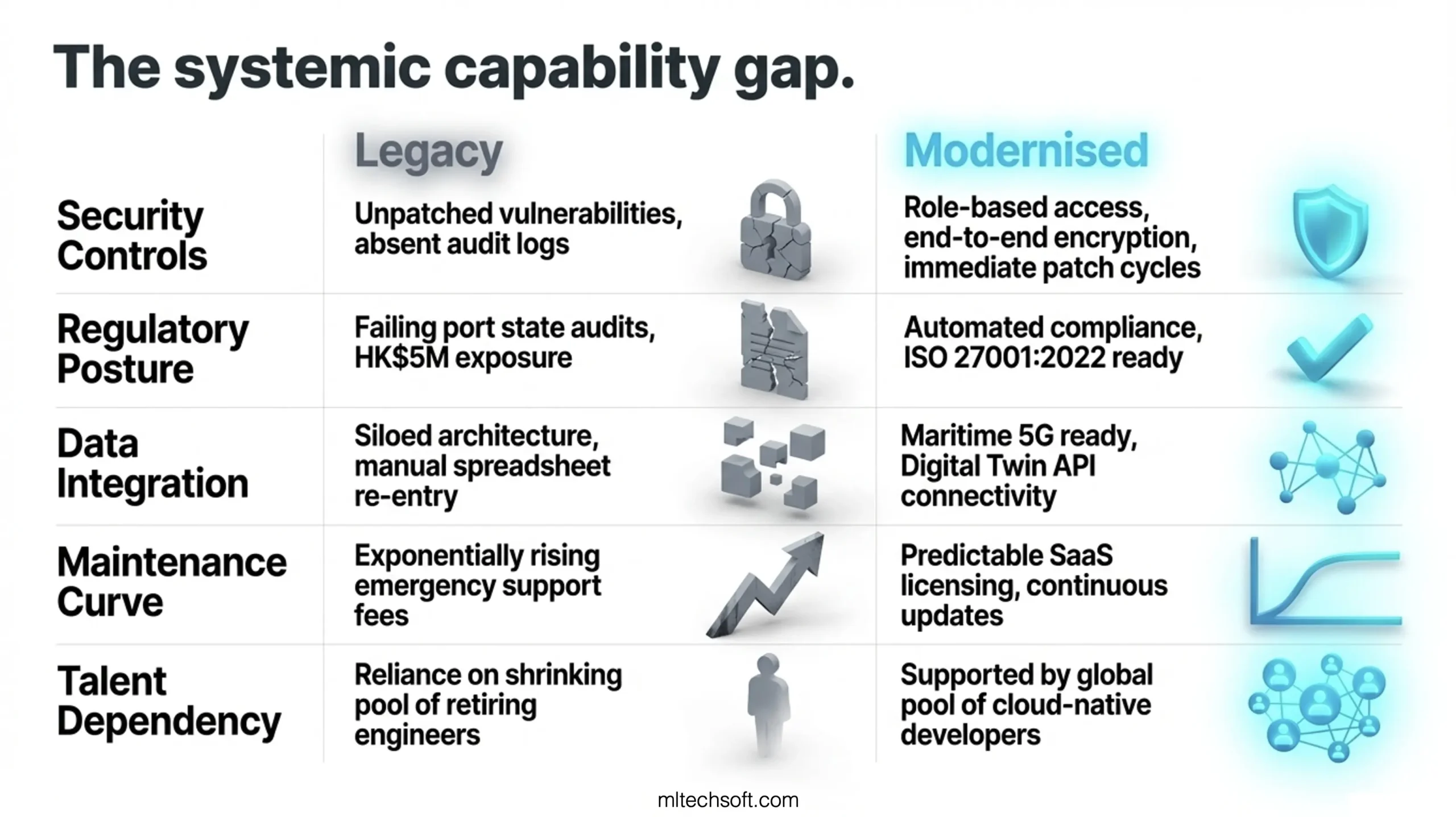
Legacy ship management software carries costs that extend well beyond the licence renewal fee. The most significant categories include emergency patch and fix costs when aging systems fail, staff productivity losses from manual workarounds, security incident exposure under IMO 2021 and the Hong Kong Critical Infrastructures (Computer Systems) Bill, compounding maintenance burden as expertise becomes scarce, and the opportunity cost of systems that cannot integrate with Singapore’s Maritime 5G and Digital Twin infrastructure.
For ship managers in Singapore, these costs have crossed the cost of modernisation in 2026.
Summary Table: The Five Hidden Cost Categories
| Cost Category | Annual Range | Driver | Impact |
|---|---|---|---|
| Emergency Fix & Patch | SGD 100–400K | Unplanned system failures, emergency vendor support | Operational disruption, crew safety risk |
| Staff Time Lost to Workarounds | SGD 150–600K | Manual data entry, non-integrated systems, process delays | Reduced operational efficiency, salary burden |
| Security Incident Exposure | SGD 250–2M+ | Unpatched vulnerabilities, regulatory fines, business interruption | Compliance violations, reputational damage |
| Compounding Maintenance Burden | SGD 200–800K | Shrinking vendor expertise, rising support costs, legacy infrastructure sprawl | Reduced system reliability, vendor lock-in |
| Opportunity Cost of Delayed Modernisation | SGD 300–1.2M | Missed integration with Digital Twin, Maritime 5G, fleet analytics; competitive disadvantage | Inability to compete on operational efficiency |
Emergency Fix and Patch Costs
Emergency fix costs average 2–5 times the cost of planned maintenance. When a legacy ship management system fails without a support contract in place, operators are forced into emergency vendor negotiations with zero pricing leverage. A four-hour downtime affecting crew roster management, bunkering schedules, or compliance reporting can halt operations and trigger regulatory intervention.
In our work with Singapore-based ship management clients, emergency fixes to systems older than ten years typically cost SGD 40K–100K per incident. Most organisations experience two to four unplanned failures annually. The vendor knows the system is aging and knows you’re desperate — pricing reflects that reality.
Staff Time Lost to Workarounds
Legacy systems rarely integrate seamlessly with modern enterprise tools. The result is a hidden workforce operating manual workarounds: spreadsheets that copy data from the legacy system, email-based approval chains for crew schedules, and hand-entered crew compliance records that should be automated.
A ship management company managing 60 vessels typically has three to five staff members spending 20–40% of their time on data re-entry and reconciliation. At an average maritime IT salary of SGD 80–120K annually, this translates to SGD 150–250K per employee per year — consumed entirely by operational friction that modernisation eliminates.
Most CTOs underestimate this cost because the workarounds have become invisible. They’re just “how we operate.” That invisibility is the expense.
Security Incident Exposure and Regulatory Risk
This is the cost that keeps maritime CTOs awake. Legacy systems built before 2015 lack the architectural controls modern security requires: role-based access controls, encryption at rest and in transit, audit logging, and the ability to patch vulnerabilities in months rather than years.
According to the 2025 maritime cyber threat report from CYTUR, operational systems became explicit attack targets in 2025 — not just data theft, but direct attempts to manipulate voyage data, disable alarm systems, or compromise crew management systems. A successful attack on crew roster data can ground vessels and expose the operator to flag state enforcement action.
The Hong Kong Critical Infrastructures (Computer Systems) Bill, enforced from 1 January 2026, imposes mandatory cyber risk management requirements on maritime operators. Failure to demonstrate compliance with modern security standards carries fines up to HK$5 million. Legacy systems cannot meet these requirements; modernised systems with current authentication, encryption, and audit trails can.
Compounding Maintenance Burden
Every year a legacy system runs, the cost of maintaining it rises. Fewer vendors support aging technology. The original developers have retired or left the industry. Security patches become riskier because the codebase is no longer understood.
A system that cost SGD 50K to maintain annually in year five of operation might cost SGD 150K by year fifteen. The maintenance curve turns exponential. By the time a decision is finally made to modernise, maintenance costs have become so high that they’re actually financing the replacement.
Opportunity Cost of Delayed Modernisation
Singapore’s Maritime Digitalisation Playbook has established that the next generation of competitive advantage lies in data integration and real-time visibility: vessel positioning, crew health monitoring, bunkering optimisation, and compliance automation all feeding into a unified Digital Twin. Maritime 5G infrastructure is being deployed at major ports.
Legacy systems cannot participate in this ecosystem. They cannot share data with Maritime 5G sensors. They cannot integrate with Digital Twin platforms. They cannot consume real-time port state data or voyage optimisation algorithms. While competitors modernise their vessel management systems, legacy operators remain locked in 2010-era workflows, unable to access the tools that drive operational efficiency in 2026.
The Regulatory Cascade: Why IMO 2021, NIS2, and the Hong Kong Critical Infrastructures Bill All Converged in 2026
Three regulatory mandates converged in 2026, each independently requiring legacy systems to be evaluated, and collectively making that evaluation unavoidable:
IMO 2021 (Consolidated Cyber Risk Management Framework). The International Maritime Organization’s MSC-FAL.1/Circ.3/Rev.3 — implemented fully across flag states in 2024–2025 — requires vessel operators to demonstrate that their ship management systems protect against cyber incidents. Port state control inspections now include cyber risk assessments. A system that cannot demonstrate patching, access control, or incident response readiness will fail inspection and restrict port access.
NIS2 (Network and Information Security Directive 2022/2555). The European Union’s NIS2 Directive, transposed into national law across member states by 2025, extended mandatory cyber reporting and incident notification requirements to maritime operators. Any operator with significant EU trade exposure must demonstrate compliance. Non-compliance carries penalties of 4% of annual global revenue.
Hong Kong Critical Infrastructures (Computer Systems) Ordinance, enforced 1 January 2026. Hong Kong classified maritime transport as a designated critical infrastructure sector, requiring operators to adopt “appropriate measures” to protect computer systems from cyber risk. The Code of Practice, issued simultaneously with the Ordinance, references ISO 27001:2022 as the reference standard for technical controls. Failure to comply carries fines up to HK$5 million.
For a Singapore ship manager with a global fleet and Hong Kong trading partners, all three requirements apply. Each independently would justify a software modernisation project. Together, they create a synchronized compliance deadline: 2026 is the year every ship management company must have executed or committed to a modernisation plan.
Waiting until 2027 or 2028 means operating under regulatory scrutiny with systems known to be non-compliant — a position no board will accept after the regulatory clarity of 2026.
The Talent Problem: The Developers Who Know Your Legacy System Are Retiring
Legacy ship management software platforms — systems built in the 1990s and 2000s — are increasingly operated by aging teams. The core developers who built and understood these systems are retiring. The next generation of maritime software engineers was trained on cloud platforms, APIs, and modern security frameworks, not on legacy mainframe-connected systems.
This creates a structural shortage. When your legacy system needs a critical fix, you need someone who understands its architecture. That person is increasingly scarce and increasingly expensive. If that person retires or leaves before modernisation is complete, you have a system nobody fully understands running mission-critical operations.
The market responds rationally: the remaining experts charge premium rates. What cost SGD 15K for a fix in 2020 costs SGD 50K in 2026 because the pool of people who can perform it has shrunk 60%. By 2028, it could cost SGD 100K because it’s a specialised archaeological exercise.
What Is the Modernisation Window — and Why 2026 Is the Year to Act?
The “Modernisation Window” describes the three-year period (2026–2028) when the cost of modernisation is at its minimum relative to the cost of remaining on legacy systems. Three factors define this window:
Regulatory clarity. The three converging regulations gave every ship manager an external, credible reason to modernise without internal political friction. “We have to comply with the Hong Kong CI Bill” is a stronger business case than “we should upgrade because the system is old.” 2026 is the year when compliance deadlines are still somewhat distant but undeniable. By 2027–2028, non-compliance becomes indefensible.
Vendor competition. Multiple vendors are competing for the business of modernising maritime legacy systems. If you’re evaluating replacements in 2026, you have multiple strong options. If you wait until 2028 when compliance pressure becomes acute, your options narrow and vendor pricing stiffens. Vendor pricing moves up as scarcity increases. The time to negotiate is when you have alternatives.
Declining legacy support costs. Once significant portions of the industry modernise, legacy system support becomes even more specialized. The cost of patches, vendor support, and emergency fixes continues its exponential curve upward. The window to exit is narrowing.
Talent availability. The developers who can execute a safe migration away from legacy systems are still in the market in 2026. By 2028–2029, they’re employed on other modernisation projects. Starting the project in 2026 means you access available talent. Starting in 2028 means bidding for scarce resources.
CTOs we work with at MLTech Soft consistently describe 2026 as the inflection point. Compliance is undeniable. The market is competitive. Legacy costs are rising. The business case is clear. Waiting another year or two doesn’t improve any of these conditions — it weakens all of them.
How to Present the Modernisation Business Case to Your CFO
CFOs care about two things: quantified risk and quantified return. Here’s a one-page framework that works.
A One-Page Business Case Framework for Ship Management CTOs
MODERNISATION BUSINESS CASE SUMMARY
1. COST OF INACTION (Annual Risk Exposure)
- Emergency repairs & unplanned downtime: SGD 250–500K
- Staff time lost to workarounds: SGD 150–300K
- Regulatory fine exposure (Hong Kong CI Bill, IMO 2021): SGD 500K–2M
- Maintenance cost inflation (legacy systems): SGD 100–200K
─────────────────────────────────────────────
ANNUAL INACTION COST: SGD 1–3M
2. COST OF ACTION (Modernisation Project)
- Software licence & implementation: SGD 800K–2M
- Data migration & testing: SGD 200–500K
- Team training & change management: SGD 100–250K
─────────────────────────────────────────────
ONE-TIME PROJECT COST: SGD 1.1–2.75M
PAYBACK PERIOD: 4–8 months
3. COMPLIANCE READINESS
- Current IMO 2021 compliance status: NON-COMPLIANT
- Regulatory risk window: CLOSING (1 Jan 2026)
- Hong Kong CI Bill exposure (if applicable): HK$5M fine risk
4. STRATEGIC UPSIDE
- Integration with Digital Twin: UNLOCKED post-modernisation
- Maritime 5G ecosystem readiness: ENABLED
- Operational efficiency gain: 15–30% estimated
This framework reframes modernisation from a cost centre (IT project) to a risk-mitigation and revenue-protection decision (CFO concern). The payback period of 4–8 months — driven by eliminated emergency costs and reduced maintenance burden — is compelling. The compliance deadline removes the “we can defer this” option.
FAQ: Legacy Ship Management Software Costs and Risks
What is the average cost of an unplanned legacy system failure?
Emergency repairs to legacy systems older than ten years typically cost SGD 40–100K per incident. This includes emergency vendor support (charged at rates 3–5x normal support), workaround implementation costs, and operational downtime impact. Most ship managers experience two to four unplanned failures annually. A proactive replacement eliminates this cost category entirely.
How do regulatory deadlines affect the modernisation timeline?
The Hong Kong Critical Infrastructures (Computer Systems) Ordinance came into effect 1 January 2026. IMO 2021 compliance was mandated across flag states by 2024–2025. Both regulations now apply to any ship manager operating in Hong Kong or with flag state audit exposure. Compliance requires demonstrating modern security controls — patching frequency, encryption, access logs, incident response capability. Legacy systems typically cannot meet these standards. Modernisation projects take 12–18 months. Starting in 2026 means going live with compliant systems by Q3–Q4 2027. Waiting longer risks operating in non-compliant status, which flag states and port state control inspectors can now observe directly.
What’s the biggest hidden cost of legacy ship management software?
Staff time lost to manual workarounds. Most CTOs don’t cost this out because the workarounds are invisible — “that’s just how we operate.” But three to five staff members spending 20–40% of their time on data re-entry, reconciliation, and email-based approvals represents SGD 150–250K annually in pure operational friction. Modernised systems eliminate this through automation and integration.
Can we migrate away from legacy systems without downtime?
Yes, but it requires careful planning. The pattern is a parallel-run approach: the new system is built and tested alongside the legacy system, validated in production for 4–12 weeks, then cut over during a planned port call or operational window. This de-risks migration by proving the new system works before the old one is switched off. MLTech Soft’s approach to maritime software migration follows this pattern — we’ve executed zero-downtime cutover for Singapore-based ship managers managing complex global fleets.
What should a CTOs first step be?
Request a free maritime software assessment. A structured evaluation identifies unpatched vulnerabilities, compliance gaps, and hidden workaround costs specific to your operation. This assessment becomes the foundation for the internal business case — it’s not a sales pitch, it’s a risk inventory. Once the inventory is clear, the CFO conversation becomes straightforward: “Here’s what the system is costing us annually. Here’s what compliance requires. Here’s what modernisation costs. Here’s the payback period.”
Conclusion
Legacy ship management software was fit for purpose in 2010. It isn’t fit for purpose in 2026. The decision isn’t whether to modernise — it’s whether to act while you have runway, vendor choice, and talent availability, or to be forced into emergency replacement when regulatory pressure becomes acute and costs have tripled.
The Modernisation Window is real. The window is closing. And 2026 is the year when every ship management CTO will make this choice.
The companies that choose to act now will spend 2026 building compliant, integrated, efficient systems. The companies that defer will spend 2027 and 2028 explaining to their boards why they’re operating under regulatory scrutiny with systems they know need to be replaced.
Next Step: Get Your Maritime Software Assessment
The first step is clarity. Request a free maritime software assessment from MLTech Soft. In one hour, we’ll map your current system’s risk exposure across the five cost categories, identify compliance gaps specific to your operation, and give you a prioritised modernisation roadmap — with no sales pitch, just honest assessment.
The only worse choice than modernising in 2026 is realising in 2028 that you should have.
Request a free maritime software assessment
Self-Audit Checklist: Is Your Ship Management Software Exposing You to These Costs?
Use this checklist to evaluate your current exposure:
[ ] Your primary ship management system was last significantly updated more than 5 years ago
[ ] You have experienced 2+ unplanned system failures in the past 12 months
[ ] Your team uses spreadsheets or manual workarounds to move data between systems
[ ] Crew roster, maintenance, or compliance reporting involves email approvals or hand entry
[ ] You cannot document the current patching status of your system
[ ] Your system vendor no longer actively develops new features for your version
[ ] Integration with external systems (port state data, bunkering systems, etc.) is done via manual export/import
[ ] Your core developers or system operators have announced retirement or departure in the next 2 years
[ ] You have not conducted a formal cyber risk assessment in the past 2 years
[ ] You cannot point to a specific person who understands the full architecture of your system
Score: 0–2 checked boxes → Your system is likely in good operational health. Continue monitoring.
Score: 3–5 checked boxes → Your system is showing age. Plan a formal assessment within 6 months.
Score: 6+ checked boxes → Your system is a material business risk. Initiate a modernisation evaluation immediately. Do not wait until 2027.
Table of Contents






