The three earliest warning signs that maritime software is becoming a compliance liability are behavioural, not technical: vendor response time on security and audit questions has materially stretched, operational workarounds have grown faster than the system has changed, and the same audit finding is reappearing across cycles in slightly different language. Any one is noise. Two firing simultaneously is the threshold at which Singapore ship managers should run a structured compliance assessment, before the next class survey or ISM audit forces the timeline.
Three signs that compliance trouble has already started
Technical audits surface software problems too late. By the time a class survey or ISM audit names a software-driven non-conformity, the warning signs were visible inside the organisation for 6–12 months — and observable without external help.

| Sign | What it looks like | What it predicts |
|---|---|---|
| Vendor response latency | Compliance queries that used to come back in days now take weeks | Vendor evidence pack won’t assemble at survey speed |
| Workaround proliferation | Spreadsheets, Outlook calendars, manual exports running parallel to the system of record | Audit evidence lives outside the system; reconstruction will fail |
| Recurring audit findings | Same root cause re-described and re-closed across two or more cycles | Tolerated risk converts to non-conformity at the next cycle |
So what? None of these require a forensic audit to spot. They are observable from an hour reviewing emails, a 30-minute conversation with three superintendents, and a stack of internal audit reports.
Sign #1: Vendor response latency
The first sign is in your inbox. A vendor who responded to security queries within a working week now takes three weeks — or deflects to “the next release.” The pattern is gradual; the team adapts and stops noticing.
A vendor that cannot — or will not — respond on compliance questions is either resource-constrained, deprioritising you, or hiding a gap. None produce a clean audit pack. The IACS UR E26 evidence pack a surveyor asks for cannot be assembled at speed when routine queries take weeks.
Diagnostic test (under one hour): Pull the last 12 months of email exchanges with the vendor on any security, audit, patch, or version question. Calculate average response time. If it has more than doubled since contract signing, this sign is firing.
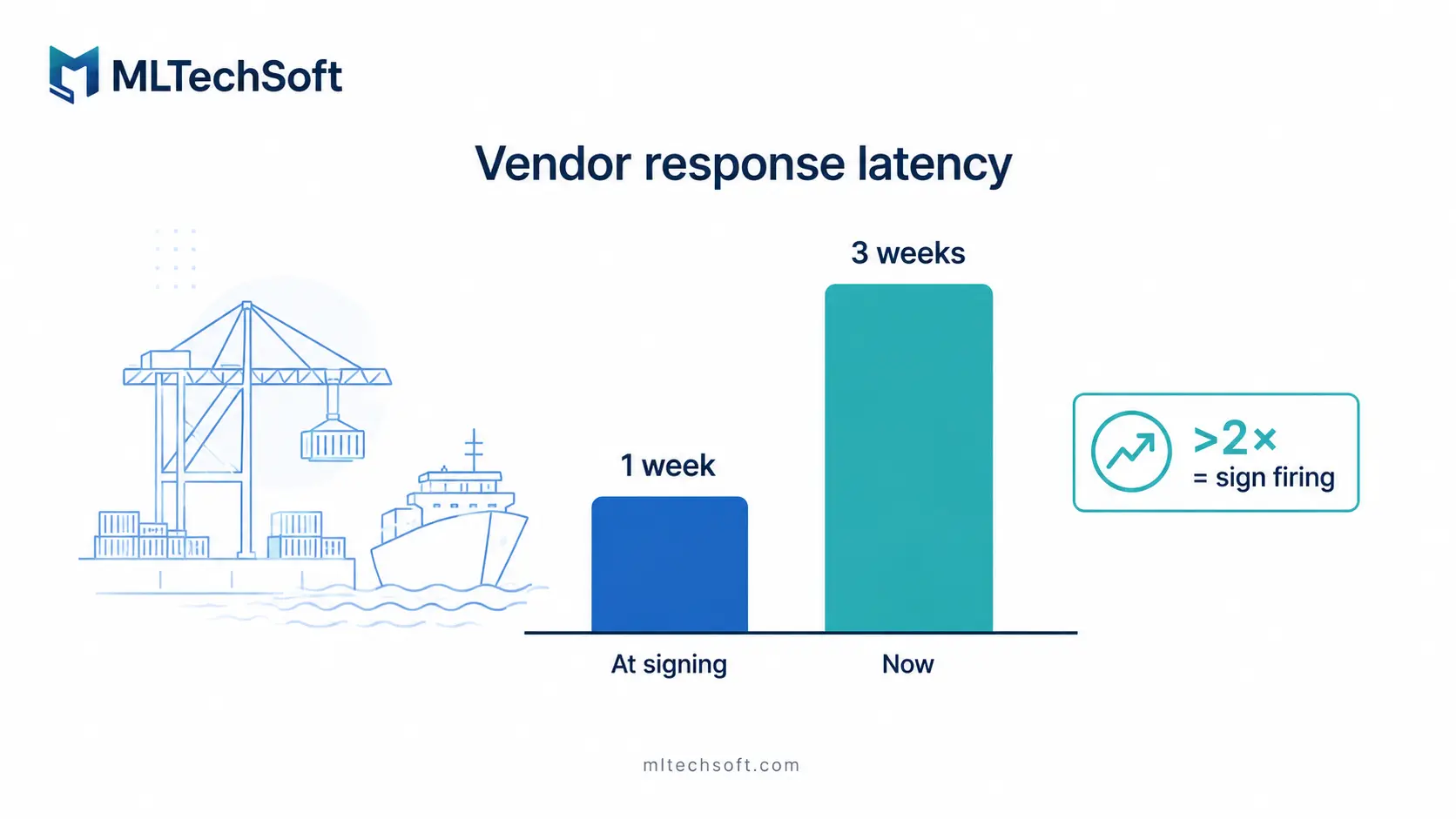
So what? Vendor response time is the earliest reliable predictor of a compliance trajectory.
Sign #2: Workaround proliferation
The second sign is in daily practice. Crew rest hours tracked in a parallel spreadsheet because “the system is buggy.” Planned maintenance in Outlook because “it’s faster.” Reports exported and reformatted manually. Each was a sensible local fix; the aggregate is a record-keeping system outside the system of record.
When the auditor asks for evidence under ISM, MLC 2006, or the cyber risk annex of the SMS, the workaround becomes the evidence. Most workarounds are not retained, version-controlled, or auditable. An MLC 2006 rest-hours audit will not accept “we keep a spreadsheet on the chief mate’s laptop” as an explanation for PMS data gaps.
Diagnostic test (under one hour): Ask three superintendents to walk you through one compliance-relevant task — rest hours review, maintenance signoff, or incident escalation. Count the steps that happen outside the official software. More than two for any task, and this sign is firing.
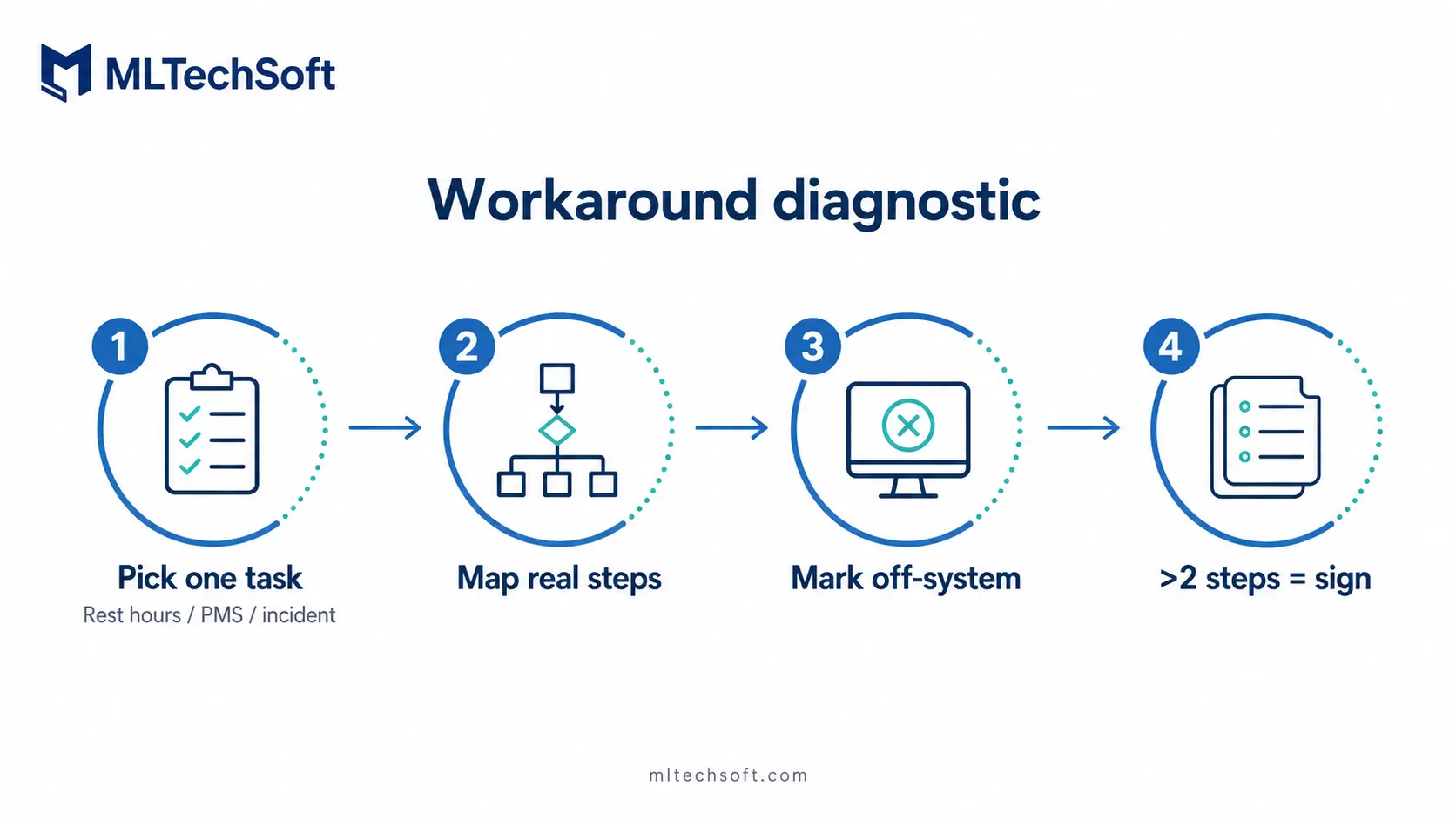
So what? Workarounds are how your team tells you, without saying it, that the software no longer matches the work.
Sign #3: Recurring audit findings
The third sign is in the audit reports. This year: “incomplete maintenance evidence in the PMS.” Two cycles ago: “inconsistent record-keeping in the maintenance system.” Three cycles ago: “manual entries in maintenance logs not corroborated by system data.” Different words, same root cause.
A recurring finding is not a finding — it is a tolerated risk. ISM auditors and IACS surveyors increasingly cross-reference internal audit reports during in-service surveys and look for repeat findings as evidence of inadequate root-cause action.
Diagnostic test (under one hour): Pull the last three internal audit reports. Highlight any finding related to a software system. Cluster them by underlying cause. If a single root cause has been re-described and re-closed across two or more cycles, this sign is firing.
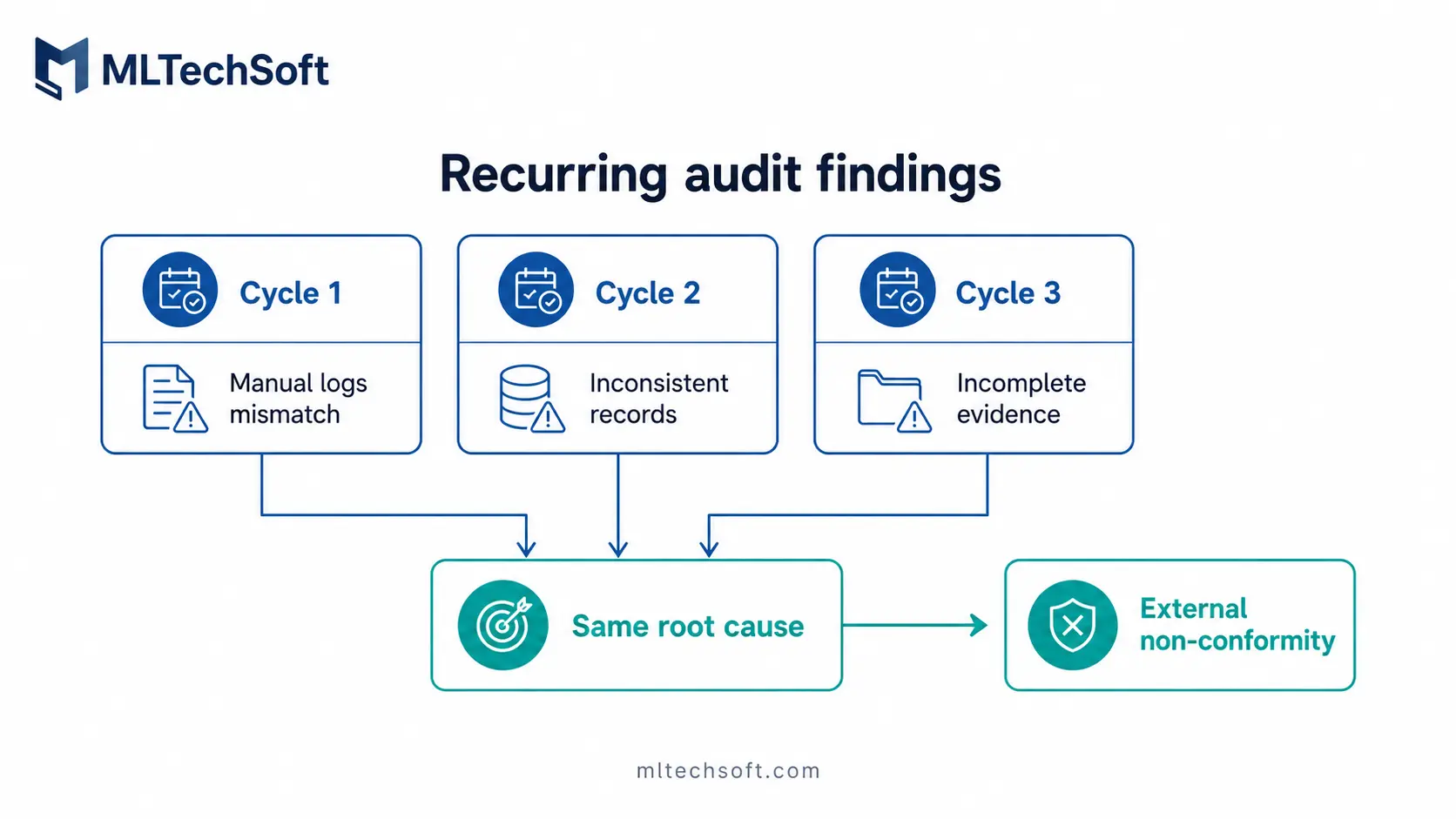
So what? The third recurrence is usually when the finding escalates externally — and it does not escalate gradually.
The two-of-three rule
The rule: One sign is noise. Two is the action threshold. Three is a finding waiting to happen.
One sign firing is normal noise. Document it, monitor it, raise it at the next quarterly review.
Two of three means the system is on a compliance trajectory. Run a structured assessment now, before the next audit cycle locks in the timing.
Three of three means the next external finding will be material. Plan a replacement or a structured remediation; do not wait for the audit to force the timeline.
Important caveat: not every warning sign requires immediate action. Some estates legitimately operate with one persistent sign for years — particularly where the system handles non-compliance-relevant data or the vendor has communicated a known constraint transparently. The rule is about pattern recognition, not reflexive replacement.
So what? Use this the way you would use any other risk threshold. The decision is not “should we replace?” — it is “should we run a structured assessment this quarter or next?”
What this looks like in practice
A Singapore-based ship management company managing 25+ vessels operated under all three signs for nearly nine months before acting. Vendor response time on patch queries had tripled. Three workarounds were active across rest hours, planned maintenance, and incident reporting. The same maintenance evidence finding had appeared in two consecutive internal audit cycles, closed both times with corrective actions that did not address the root cause.
The decision to wait was rational — the vendor relationship was older than the system, and both sides had reasons to preserve it. The team agreed to give the vendor “one more cycle.”
The next external audit produced a non-conformity requiring a six-week corrective action plan and a re-baselining project under regulatory pressure. MLTech Soft’s ISO 27001:2022-certified maintenance practice covered the vendor evidence consolidation, patch log reconstruction, and incident response rewrite. It cost roughly three times what an earlier structured assessment would have, on the auditor’s timeline.
So what? Acting on two of three costs a structured assessment. Waiting until three of three plus an external finding costs a remediation under regulatory pressure. The ratio is not subtle.
FAQ: Maritime software compliance risk questions answered
How can I tell if my maritime software is putting my SMS at risk?
The earliest signals are behavioural: vendor response time on compliance queries, the proliferation of operational workarounds, and the recurrence of audit findings on the same root cause. Each can be diagnosed in under an hour. Two firing simultaneously is the threshold for commissioning a structured assessment.
What’s the difference between a workaround and a non-conformity?
A workaround is a local adaptation by the team when the system does not match the work. A non-conformity is the auditor’s formal finding that the SMS fails to meet the applicable standard. The link is direct: a workaround that holds compliance-relevant data outside the system of record almost always produces a non-conformity when the auditor asks for that data.
When does a recurring internal audit finding become a class survey issue?
Typically by the third cycle. ISM auditors and IACS surveyors cross-reference internal audit reports during in-service surveys and look for repeat findings as evidence of inadequate root-cause action under the SMS. A finding closed twice with corrective actions that did not address the underlying cause is read as a signal that the SMS is not actively managing the issue.
Should we replace a non-compliant maritime system or remediate it?
It depends on which signs are firing and which root cause sits underneath. If the vendor is responsive and workarounds are recent, remediation is usually faster and cheaper. If vendor latency has been stretching for over a year and audit findings have recurred across multiple cycles, replacement is often the only path that closes the underlying issue. A structured assessment should always precede the decision.
What to do this quarter
Diagnose your own estate. Pull the vendor email exchanges. Walk three superintendents through their compliance-relevant tasks. Read the last three internal audit reports. The exercise takes an afternoon, requires no external help, and produces a clear answer: are you carrying one warning sign, two, or three?
If two or more are firing, MLTech Soft offers a free 1-hour structured software compliance assessment. We work through the same diagnostic — vendor response logs, workaround inventory, recurring audit findings — and produce a written gap list with a recommended action sequence ahead of your next external audit. Book your compliance assessment →
Table of Contents






