Maritime software liability risk refers to the measurable financial exposure created by aging, under-maintained, or non-compliant software systems in maritime operations. Unlike a one-time maintenance cost, this liability compounds over time — security vulnerabilities accumulate, regulatory gaps widen, and the institutional knowledge needed to fix problems quietly leaves with every staff departure. For Singapore ship managers, the combined annual cost of unaddressed software liability typically ranges from SGD 1–3M, a figure that rarely appears in IT budgets but shows up unmistakably in audit findings, emergency repair invoices, and cyber incident response bills.
Why “Technical Debt” Is the Wrong Name for What You’re Carrying
Most IT discussions frame aging software as “technical debt” — a metaphor borrowed from finance. Debt implies something you can carry at a fixed interest rate, restructure when convenient, or write off when the cost becomes too high. It doesn’t describe what actually happens to software problems in maritime operations.
Debt is static. A maritime software liability compounds.
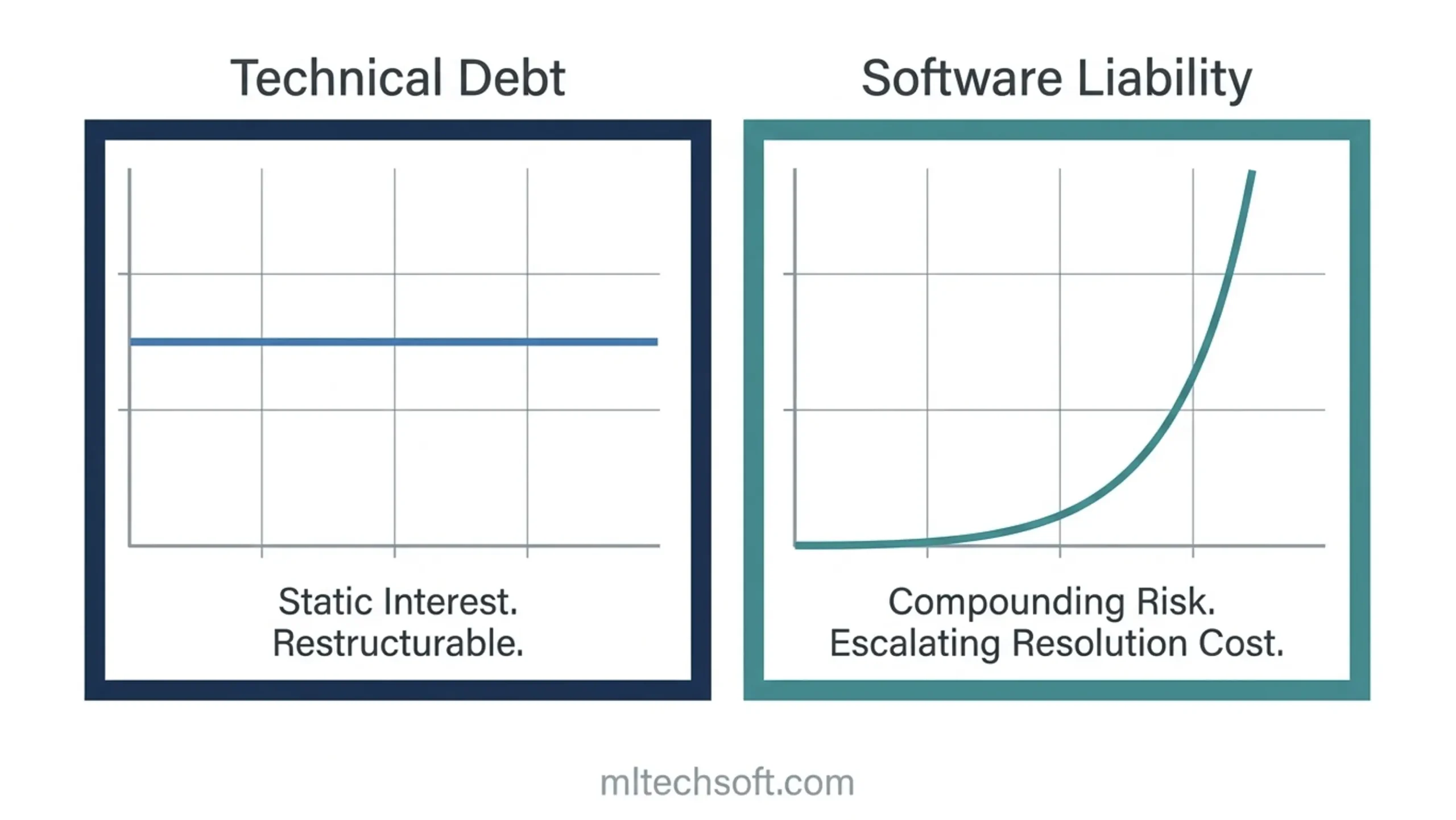
A ship management system that costs SGD 50,000 a year to maintain in year five of its life might cost SGD 150,000 a year by year fifteen — not because the vendor raised their prices significantly, but because the regulatory requirements have shifted, the systems around it have changed, and the engineers who understood its internal logic have moved on. Each year of deferral doesn’t add another year of the same cost. It raises the eventual cost of resolution.
This isn’t hypothetical. Based on assessments of ship management systems in Singapore, the jump from manageable maintenance expense to crisis-level exposure typically happens between years eight and twelve. The system still works. It just costs progressively more to keep working — and nobody notices the gradient because each year’s cost increase looks modest compared to the previous year.
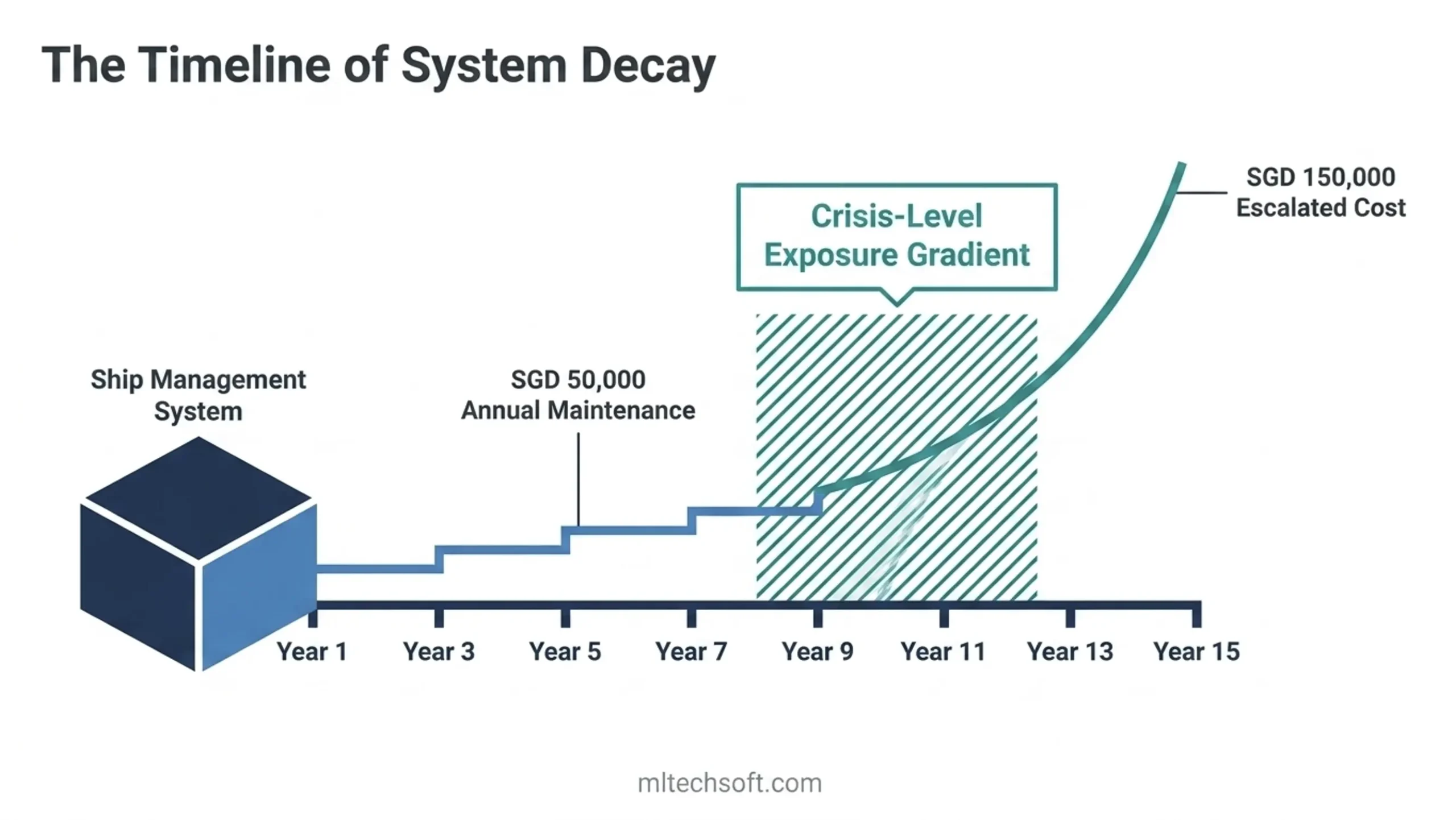
What this means for you: If your primary ship management software is more than seven years old and hasn’t had a structured modernisation review, you’re almost certainly already on the compounding curve. The question isn’t whether to act — it’s whether to act now or later with a clear-eyed view of what “later” costs per year.
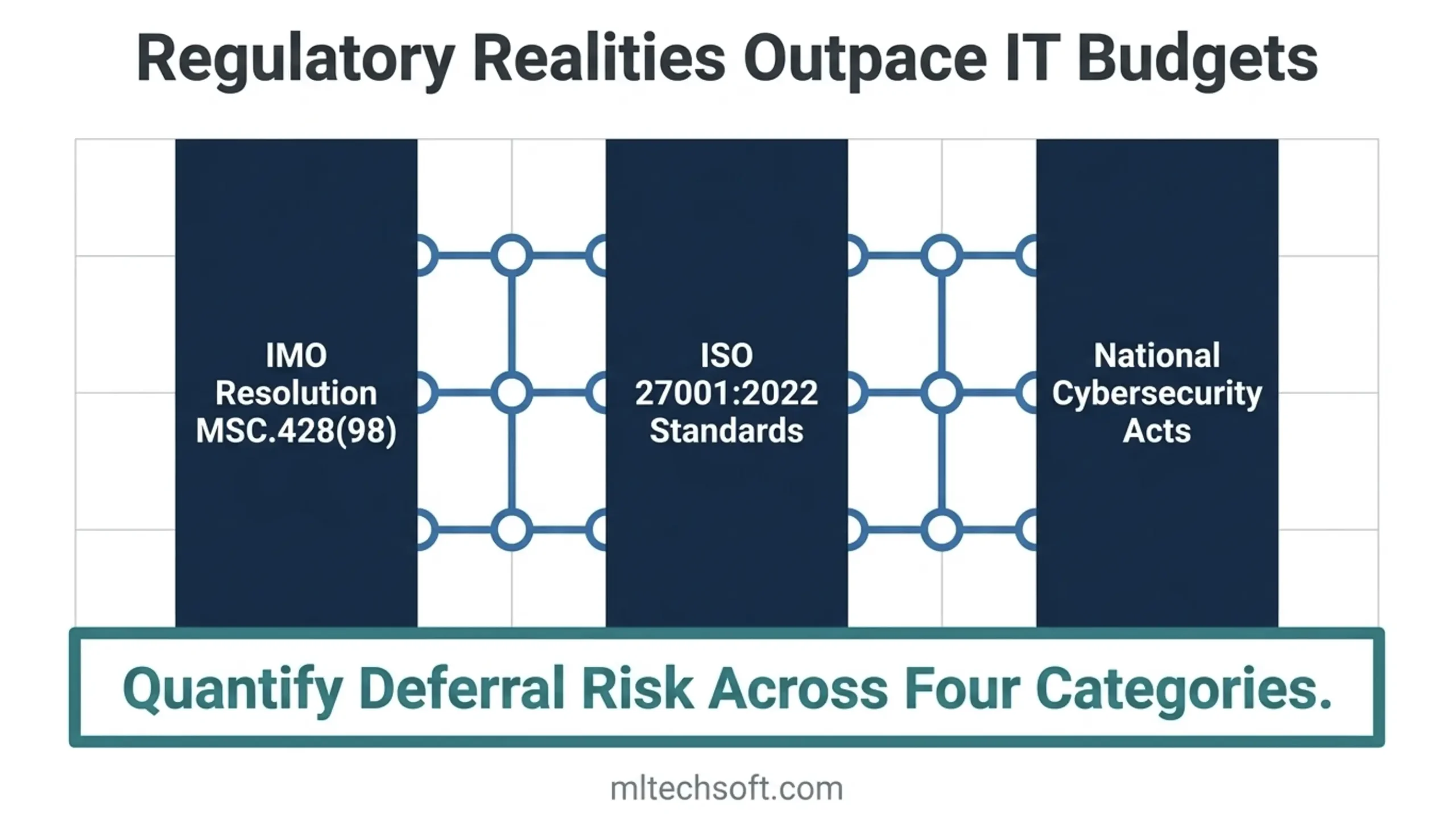
The Four Categories of Maritime Software Liability
Framing this as a single “IT maintenance problem” makes it easy to defer. Breaking it into four specific categories makes it measurable — and measurable things get budgeted.
| Category | What it is | How it compounds | Typical annual cost exposure |
|---|---|---|---|
| Security | Unpatched vulnerabilities, non-compliance with IMO MSC-FAL.1/Circ.3/Rev.3 cyber risk requirements | Each unpatched release cycle adds attack surface; post-breach costs run 10–27× the preventive investment | SGD 50–150K/year in unresolved exposure; SGD 200K–1M+ in breach scenario |
| Compliance | Gaps between system audit trail behaviour and current ISM code / IACS UR E26/E27 expectations | Class society auditors are asking increasingly specific questions about software security; gaps found late in an audit cycle are expensive to remediate under time pressure | SGD 50–200K in emergency remediation; regulatory fines up to SGD 2M under Singapore’s Cybersecurity Act for critical infrastructure operators |
| Knowledge | Loss of institutional understanding — who configured this, why it was built this way, what breaks if you change module X | Every staff departure narrows the pool of people who can troubleshoot; undocumented systems can’t be properly audited or secured | SGD 100–300K in contractor costs and extended incident resolution when something breaks |
| Operational continuity | Manual workarounds, disconnected data flows, integrations maintained by a single contractor’s custom script | Workarounds accumulate; the system can’t support new operational requirements without significant rework | SGD 150–300K in lost productivity and delayed operational improvements annually |
Most ship management IT teams can rank their exposure across these four categories in a one-hour internal conversation. You don’t need a formal audit to know whether your security patching is current, whether your last ISM annual verification raised software-related findings, or whether the person who built your key integration is still reachable.
What this means for you: Run this table as a rough self-assessment. Put a number next to each category — even a range. That exercise, done honestly, tends to produce a document that looks less like an IT issue and more like a CFO conversation.
How Software Liability Compounds — The Math Your IT Budget Doesn’t Show
Here’s what the compounding curve looks like in a specific case.
A Singapore-based ship management company managing 22 vessels operated a fleet maintenance system that had been live since 2012. Annual maintenance cost in 2018: SGD 48,000. By 2024, that figure had reached SGD 127,000 — not because the vendor dramatically increased their rates, but because each year brought more emergency patches, more contractor time from the one external consultant who still understood the original configuration, and more manual workarounds as the system failed to integrate with newer tools the operations team needed.
The team hadn’t noticed the gradient. IT budgets were approved annually, and each year’s increase looked modest in isolation. Nobody ever compared the 2018 and 2024 numbers side by side.
Key stat: Maritime cyberattacks rose 103% year-on-year in 2025 — the highest annual increase on record, according to Safety4Sea. In that environment, the security liability category shifts from theoretical to operational. A ship management company with three unpatched vulnerabilities from 2022 isn’t facing a future risk. It’s carrying a present one.
The compounding problem isn’t that the system fails suddenly. It’s that the cost of fixing it grows faster than the cost of running it — until a regulatory change, a staff departure, or a security incident forces the decision that deferral was never actually avoiding.
Worth saying plainly: sometimes deferral is the right call. A modernisation project has real costs, real disruption, and real risk. The argument here isn’t that every ship manager should launch a migration project this quarter. It’s that the decision to defer should be made with the full cost of deferral on the table — not by default.
What this means for you: Build this into your next budget conversation: not “what does modernisation cost this year?” but “what does deferral cost per year, and how many more years of that rate is acceptable given where this number is heading?”
Running a Quick Liability Estimate: A 4-Question Test
A formal assessment takes time. These four questions take 30 minutes and will tell you whether your exposure is manageable or already material.
Question 1: When did your software supplier last provide a written security patch log? If you can’t name the month, your security liability category is active. Maritime software vendors operating to ISO 27001 standards maintain patch logs as a matter of course. If yours doesn’t, you can’t answer the question a class society auditor or your P&I insurer will eventually ask.
Question 2: How many manual workarounds does your operations team use to compensate for system limitations — and has that number grown in the last two years? Each workaround is an operational continuity liability. If the number has grown, the compounding has started.
Question 3: If the one person on your team who understands the system’s configuration left tomorrow, how long would it take to restore normal operations after an unexpected failure? If the honest answer is “weeks” or “we’d have to call [contractor who built it in 2015]” — your knowledge liability is material and should appear in your risk register.
Question 4: In your last ISM annual verification, did the auditor raise any findings related to your software or data management processes? A yes means your compliance liability is documented, and the timeline is one set by your auditor, not by your IT budget cycle.
Two or more unfavourable answers places your total liability estimate in the SGD 500K–2M range annually. That’s not a reason to panic — most of it is recoverable with a structured approach. It is a reason to change the framing of your next budget conversation.
What this means for you: Take these four questions into a 30-minute meeting with your IT lead this week. The answers don’t require an external assessment — they’re already known inside the organisation. What’s usually missing is a structured moment to say them out loud.
What a Singapore Ship Manager Found When They Ran This Exercise
A Singapore-based ship management company managing 25 vessels ran an informal version of this exercise before engaging MLTech Soft for a structured assessment. They expected security to be the dominant finding.
It wasn’t.
The knowledge liability category was the most significant. Their primary fleet maintenance system had been custom-configured by a contractor between 2015 and 2018. That contractor had since moved on. Three senior IT staff were on the team — none of whom could answer Question 3 in under two weeks. Two findings from the previous ISM annual verification were linked to the same system’s reporting module: a module that nobody currently employed fully understood.
The cost wasn’t visible in any single line item. It appeared as extended incident resolution time, a standing policy of “don’t change the configuration unless you know exactly what you’re doing,” and a growing set of manual reporting processes that existed because the system could no longer produce the output the auditor expected automatically.
MLTech Soft’s assessment produced a written risk register across all four liability categories. Security and compliance were both addressable within a 6-month retainer engagement. The knowledge liability required a structured documentation sprint first — something the team hadn’t anticipated, but which turned out to be the most useful output of the exercise.
The total annual cost of accumulated liability, once quantified: SGD 1.4M. The modernisation budget their CEO had approved and deferred the previous year: SGD 280,000.
What this means for you: An internal exercise takes 30 minutes. A structured assessment takes a day. Neither requires committing to a project. The output is a quantified risk register — which is precisely the document that changes a CFO’s answer from “defer” to “let’s look at the numbers.”
FAQ: Maritime Software Liability Questions Answered
How do I calculate the full cost of maintaining a legacy maritime system?
The direct maintenance cost — vendor fees, support contracts, internal staff time — is typically the smallest component. A complete picture covers: emergency repairs and unplanned downtime (SGD 250–500K for a significant incident at a mid-size operation), regulatory remediation when a compliance gap is found under audit pressure, productivity loss from manual workarounds, and security incident response. Most companies find the full cost is 2–4× their IT maintenance budget line when these categories are included.
What is the average cost of a maritime cyber incident?
Available data suggests total incident cost runs 10–27 times the investment required to prevent it. For a Singapore ship management operation, an unplanned system failure affecting daily operations for 3–5 business days carries a direct cost of SGD 100–400K in staff time, emergency contractor engagement, and operational disruption — before accounting for regulatory consequences or insurance premium adjustments. Maritime cyberattacks increased 103% year-on-year in 2025, making this an actuarial reality, not a theoretical scenario.
Is there a recognised standard for assessing maritime software security risk?
Yes. IMO Resolution MSC.428(98) and the associated guidelines in MSC-FAL.1/Circ.3/Rev.3 establish the framework for cyber risk management in maritime safety management systems. For Singapore operators, the Cybersecurity Act designates maritime as a critical information infrastructure sector — carrying mandatory obligations and fines up to SGD 2M for non-compliance. ISO 27001:2022 provides the operational security standard against which software suppliers can be independently assessed. When evaluating a software vendor or running an internal assessment, these three frameworks define what “adequate” looks like from a regulator’s perspective.
If you’re building a budget case for software investment and need an honest assessment of what your current system is actually costing, MLTech Soft offers a free 1-hour maritime software assessment — producing a written risk register across all four liability categories. [Book your free assessment at mltechsoft.com.]
Table of Contents