Opening: The Direct Answer
ISO 27001 has become a minimum requirement for maritime software vendors because IMO’s updated cybersecurity guidelines (MSC-FAL.1/Circ.3/Rev.3, April 2025) explicitly require ship managers to assess and manage the cyber risk of their third-party software suppliers. ISO 9001, which certifies quality management processes, does not address information security — and accepting it as a security credential transfers the vendor’s cyber risk to the ship manager. A vendor handling crew records, voyage data, and compliance documentation must hold ISO 27001 certification covering their software development and maintenance scope.
The distinction has moved from “best practice” to “regulatory accountability.” If your software vendor suffers a breach and your cyber SMS audit reveals you never verified their security credentials, the port state control authority will hold your ship management company responsible.
What Changed in April 2025: The IMO’s Updated Cybersecurity Guidelines
On April 4, 2025, the International Maritime Organization published MSC-FAL.1/Circ.3/Rev.3 — the most significant update to maritime cyber guidance since IMO Resolution MSC.428(98) in 2017. The update is not incremental; it fundamentally shifts how ship managers must approach third-party software supplier risk.
The key change is alignment with NIST Cybersecurity Framework v2.0. The earlier 2017 resolution referenced NIST CSF v1.0. The shift to v2.0 brings updated governance requirements, expanded accountability for supply chain risk management, and explicit language requiring organizations to assess and manage the cyber risk of their third-party suppliers.
For ship managers, this has one critical implication: you are now explicitly accountable for your software vendor’s cyber posture. You cannot claim ignorance or operational necessity. The guideline states plainly that ship managers must “verify that external service providers implement appropriate cyber risk management measures commensurate with the risk level they handle.”
In practical terms, this means:
- You must document how you evaluated your vendor’s security credentials.
- You must retain evidence of that evaluation for port state control audits.
- If a breach occurs at the vendor level and your SMS audit shows you accepted unverified claims about their security, you carry regulatory liability.
This is not a vendor problem anymore — it’s a ship manager problem.
ISO 9001 vs ISO 27001: Why They Are Not Interchangeable
This is the distinction that trips up most maritime operators. Multiple vendors will claim ISO certification, and if you’re not precise about which standard, you will accept insufficient security credentials.
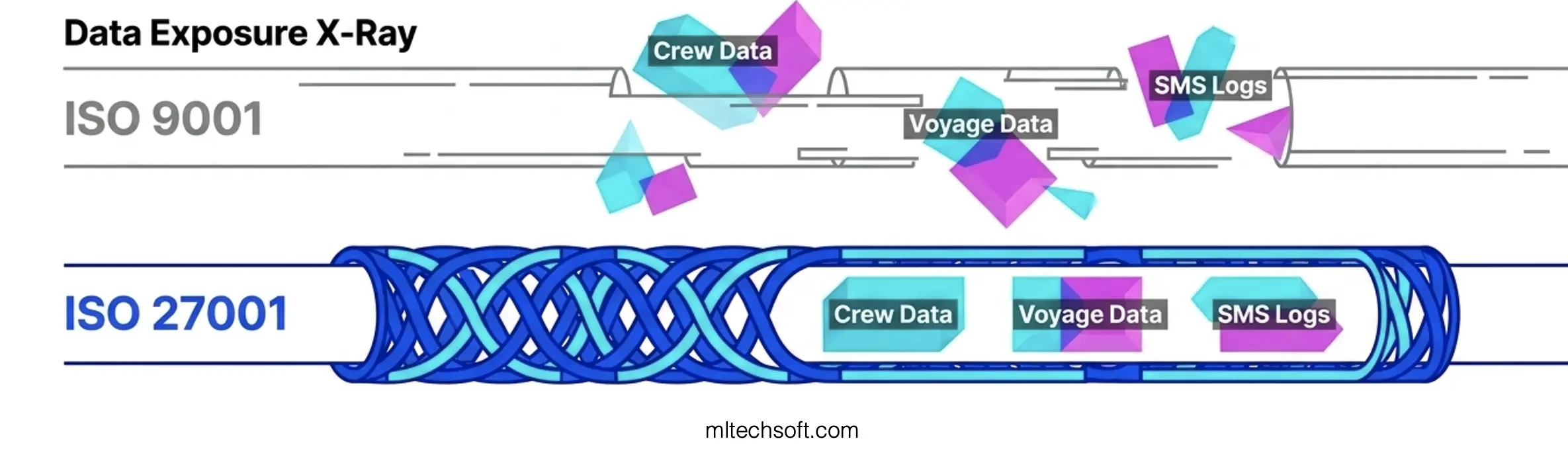
ISO 9001:2015 certifies a quality management system. It evaluates whether a vendor has documented processes, training standards, change control procedures, and delivery consistency. It does not address cybersecurity. An ISO 9001 auditor asks: “Do you have a change management process?” and “Are your staff trained on this process?” They do not ask: “How is customer data encrypted?” or “What penetration testing do you conduct?”
ISO 27001:2022 certifies an information security management system (ISMS). It evaluates whether a vendor has implemented encryption protocols, access control frameworks, incident response procedures, penetration testing regimes, data residency policies, and breach notification procedures. An ISO 27001 auditor asks: “How is client data protected during transmission?” and “What is your incident response timeline?” — the questions that matter for security.
Here is the clearest way to understand the difference:
| Dimension | ISO 9001:2015 | ISO 27001:2022 |
|---|---|---|
| Focus Area | Quality management and delivery consistency | Information security and data protection |
| What It Protects | Process integrity; customer experience | Customer data; confidentiality, integrity, availability |
| Audit Scope | Documentation, training, process adherence, customer feedback | Encryption, access control, penetration testing, incident response, physical security |
| Relevance to Crew Records | None — ISO 9001 does not address how crew data is stored or accessed | Critical — ISO 27001 evaluates who can access crew records and how that access is monitored |
| Relevance to Voyage Records | None — ISO 9001 covers delivery, not security | Critical — ISO 27001 certifies how voyage data is encrypted and whether unauthorized access is detected |
| IMO Compliance | Does NOT satisfy MSC-FAL.1/Circ.3/Rev.3 requirements | Required — explicitly fulfills IMO directive to verify supplier cyber risk management |
A vendor with ISO 9001 might deliver software on time, with excellent documentation, and have zero cybersecurity practices. A vendor with ISO 27001 has demonstrated, audited controls over encryption, access, and incident response — the controls that protect your data.
Many maritime software vendors hold ISO 9001 because it is less rigorous and less expensive to maintain. If a vendor pitches you ISO 9001 as a security credential, they either don’t understand the standards or they’re hoping you don’t.
Why This Distinction Matters for Ship Management Specifically
Maritime software is not generic business software. Your vendor has access to crew records (names, nationalities, certifications, medical clearances), voyage data (routes, cargo manifests, port calls), and compliance documentation (SMS records, maintenance logs, audit trails). This is not financial data or trade secrets — it is personal data and operational data with direct regulatory and insurance implications.
Who is accessing this data at your vendor’s development centre? Under ISO 27001, access is role-based, monitored, and logged. Under ISO 9001 alone, there is no requirement that controls this at all. A developer building new features might have unrestricted access to your production databases. A temporary contractor might be able to download crew records for testing. None of this would violate ISO 9001.
Maritime P&I insurers are now asking these questions. Renewal questionnaires from major insurers (e.g., Gard, Skuld, West of England) now include sections on third-party software supplier security credentials. If your vendor suffers a breach and your insurer discovers you selected them without verifying ISO 27001 coverage, your claims outcomes may be affected.
Flag states are beginning to verify this during cyber SMS audits. Port state control authorities, following the IMO’s April 2025 guidelines, are asking ship managers to produce vendor security assessments during cyber SMS audits. “Do you have evidence that you evaluated your software vendor’s cyber posture?” is becoming a routine audit question. If your answer is “the vendor mentioned they’re ISO certified,” the auditor will ask which standard — and “ISO 9001” will not satisfy the requirement.
The industry is moving in this direction. Major ship management companies like Wilhelmsen Ahrenkiel have achieved ISO 27001 certification themselves, signaling that this is becoming the baseline expectation for operators. When a ship manager holding ISO 27001 is evaluating software vendors, they are naturally requiring the same standard from their suppliers.

How to Verify a Vendor’s ISO 27001 Certification
A certificate hanging on a website is not sufficient evidence. You must verify four specific things:
1. Confirm the Scope Document
Request the vendor’s ISO 27001 scope document. This states exactly what the certification covers. Does it include “software development and maintenance,” or does it only cover “back-office IT operations” or “administrative processes”?
If the scope does not explicitly include software development and maintenance activities, the certification provides no assurance about how client data is handled during development. This is the most common failure point — a vendor holds ISO 27001, but the certification applies only to their internal operations, not to their delivery of software to clients.
2. Verify the Certification Body is Accredited
The certifying body must be accredited by a recognized accreditation body. The major accreditation bodies for ISO 27001 are:
- UKAS (UK Accreditation Service)
- DAkkS (Akkreditierungsstelle Deutscher Kalibrierdienste, Germany)
- JAB (Japan Accreditation Board)
Certification bodies like DNV, Bureau Veritas, and Lloyd’s Register are credible because they hold accreditation from one of these bodies. If the certificate does not name the accreditation body, ask the vendor directly — a legitimate certification body will provide this information freely.
3. Check the Certificate Date and Standard Version
Verify that the certificate references ISO 27001:2022, the current version. ISO 27001:2013 is superseded; if a vendor is still operating under the older standard, they have not updated their ISMS to reflect current control requirements.
The certificate should have been issued or recertified recently (within the past 3 years for ISO 27001 cycles). If the certificate is dated 2021 and has not been recertified, it is approaching expiry.
4. Request the Statement of Applicability (SoA)
The Statement of Applicability is a document that lists which of the 114 ISO 27001 controls are implemented, which are not applicable to the vendor’s context, and why. It is the audited evidence of which controls actually govern the vendor’s operations.
A vendor who can produce the SoA has been properly audited. A vendor who hesitates or claims “confidentiality concerns” prevents sharing this document has either not been audited as thoroughly or is not confident in their scope.
This document is your single best verification tool. It answers the question: “What exactly does your ISO 27001 certification cover, and what did the auditor actually review?”
Industry Fact: Maritime cyberattacks surged 103% in 2025 — the highest annual increase on record. The majority involved compromised credentials or unauthorized access to development systems. ISO 27001:2022 certification, properly scoped, directly addresses these attack vectors.
What to Include in Your Vendor Contract to Cover Cyber Risk
ISO 27001 certification is the entry requirement, not the end of the security conversation. Your contract must specify how the vendor will manage cyber risk on an ongoing basis.
Right to Audit Clause
Your contract should include the right to audit the vendor’s security controls and access logs related to your data. This is not a routine audit — it is a contractual right to verify that the certified controls are actually being maintained. A vendor holding ISO 27001 should welcome this, because the controls are documented and auditable.
Data Breach Notification Timeline
Specify how quickly the vendor must notify you of any incident affecting your data. The EU GDPR standard is 72 hours; maritime data handling may warrant faster notification (24 or 48 hours). This clause ensures you can activate your own incident response and breach reporting obligations to insurers and port states without delay.
Data Residency and Access Control Requirements
Specify where your data is stored (geography, cloud provider, etc.) and which roles have access. This ensures that crew records and voyage data are not stored in jurisdictions where they could be subpoenaed without notification, and it limits access to development staff who need it for active work.
Penetration Testing Frequency
Require the vendor to conduct independent penetration testing at least annually, and require them to provide a summary of findings and remediation status. This ensures the certified controls are being tested in practice and not just existing on paper.
These clauses are not onerous — they formalize the controls that an ISO 27001-certified vendor should already have in place. They shift the contract from “we trust you are secure” to “we have verified your security and we are monitoring it ongoing.”
FAQ: ISO 27001 and Maritime Software Vendor Selection
Q: Does ISO 27001 certification mean the vendor will never have a breach?
A: No. ISO 27001 certifies that a vendor has implemented documented, audited controls to manage information security risk. It does not guarantee immunity from attack. However, it significantly reduces the probability of preventable breaches (e.g., unencrypted data storage, inadequate access control) and it ensures the vendor has an incident response plan in place when threats do occur. For maritime software vendors, ISO 27001 is the minimum assurance that your data will not be compromised by preventable negligence.
Q: Can a vendor be “working toward” ISO 27001 certification, or do they need to hold the certificate now?
A: “Working toward” is not acceptable under the IMO guidelines. MSC-FAL.1/Circ.3/Rev.3 requires you to verify that your supplier has implemented appropriate cyber risk management. A vendor in the process of certification has not yet been independently audited. You can engage them with a contract clause requiring certification within a specific timeline (e.g., 18 months), but you cannot accept “in progress” as a current credential. Require the certificate before go-live.
Q: My vendor has ISO 27001 for their whole company. Does that automatically cover how they handle my software project?
A: Only if the scope document includes “software development and maintenance.” If the certification covers “all IT operations” or “company-wide information security,” you need to see the scope document to confirm. Ask specifically: “Does your ISO 27001 scope include software development work performed for clients?” If they hesitate or say “yes, it’s covered,” ask for the scope document. A properly certified vendor will provide it without reservation.
Q: The vendor is offering ISO 27001 as part of the contract negotiation — should I make it a condition of award or a “nice to have”?
A: Make it a mandatory condition of award. Under the IMO framework, you cannot select a vendor without ISO 27001 covering their software development scope. It is not a differentiator or a negotiating point — it is a compliance floor. If a vendor does not hold the certification, they are not eligible for selection. If you are shortlisting vendors and some are ISO 27001-certified while others are not, the non-certified vendors should be rejected at the technical evaluation stage.
Q: What if we already have a vendor without ISO 27001? Can we retrofit the requirement?
A: Yes, but this requires a formal contract amendment and a timeline. Amend the contract to require ISO 27001:2022 certification covering software development and maintenance, with a target date for certification (e.g., 18 months from amendment). Make it a KPI with financial consequences if the deadline is missed (e.g., penalty clauses or contract termination rights). This incentivizes the vendor to prioritize certification. In the interim, implement compensating controls — more frequent security audits, tighter access restrictions, more frequent breach notification testing — to reduce your risk exposure.
Q: How do I explain this requirement to a vendor without sounding like I don’t trust them?
A: Frame it as a regulatory requirement, not a personal decision. “IMO’s updated cybersecurity guidelines require us to assess and document the cyber risk of our software suppliers. ISO 27001 certification covering your software development scope is how we demonstrate that assessment to port state control authorities. This is not optional — it is a compliance obligation for us as ship managers. We’re asking all shortlisted vendors for the same credential.” Most reputable vendors will understand this context and will either hold the certification or will be motivated to obtain it.
Conclusion
The shift from ISO 9001 to ISO 27001 as a vendor requirement reflects a broader maturation of maritime cyber governance. It is no longer acceptable to assume that a vendor is secure because they deliver software on time or because they mentioned “certification” in their proposal.
The IMO’s April 2025 guidelines make ship managers directly accountable for third-party cyber risk. Port state control authorities will ask for evidence of this evaluation. P&I insurers will factor vendor security credentials into renewal terms. Your compliance framework — your SMS, your cyber SMS procedures — will need to document how you selected and continue to monitor your software vendor’s security posture.
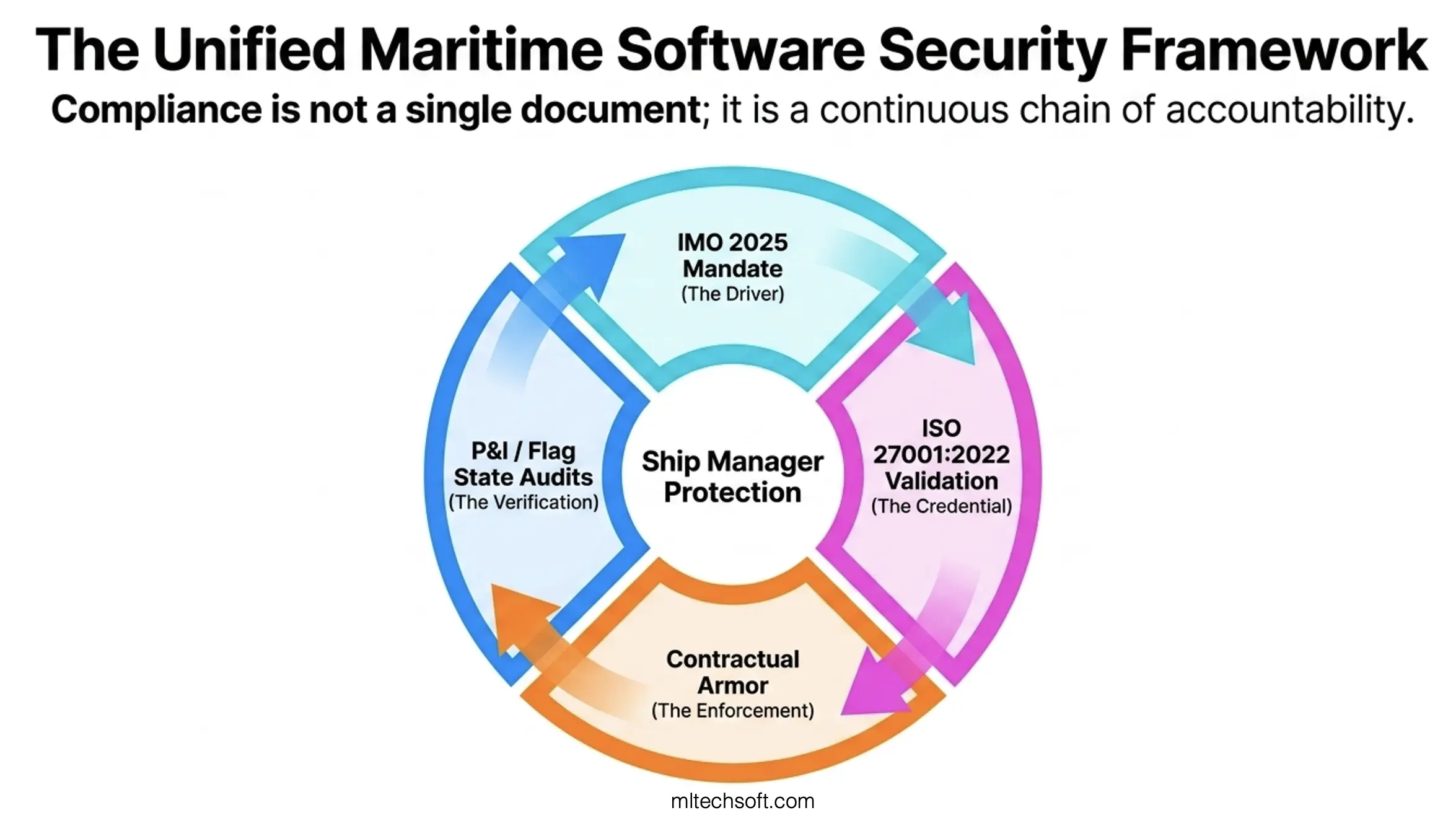
ISO 27001:2022 certification covering software development and maintenance is the threshold credential that allows you to answer these questions credibly. It is not a guarantee of perfection, but it is evidence of rigor — audited, documented controls over encryption, access, incident response, and the other foundations of information security.
If you’re evaluating maritime software vendors today, this distinction should be in your RFI (Request for Information). If a vendor cannot produce an ISO 27001:2022 scope document and Statement of Applicability, they are not ready for selection.
What You Need to Do Next
If you’re currently evaluating maritime software vendors and want to understand how to structure your security requirements — and what documentation to request from shortlisted vendors — contact MLTech Soft. We’re ISO 27001:2022 certified across our full development and maintenance scope, not just our back-office operations. We’re happy to walk you through what our certification covers, what we’d recommend asking any shortlisted vendor, and how to embed these requirements into your vendor contracts.
Contact MLTech Soft — or visit mltechsoft.com to learn more about our maritime software development and maintenance services.
Table of Contents